Secure IT Infrastructure 516150359 Online
Secure IT Infrastructure 516150359 Online establishes a critical framework for protecting sensitive information in digital environments. It employs network segmentation, strict access controls, and advanced threat detection to mitigate unauthorized access. This structured approach not only enhances operational resilience but also aligns with best practices like regular updates and continuous monitoring. Understanding its components and implementation is essential for organizations seeking to fortify their cybersecurity posture in an increasingly complex threat landscape.
What Is Secure IT Infrastructure 516150359 and Why It Matters?
A secure IT infrastructure encompasses the systems, processes, and technologies designed to protect sensitive data and maintain the integrity of an organization’s operations.
Critical components include robust cloud security measures that safeguard against unauthorized access, ensuring data protection.
This infrastructure is essential for mitigating risks, enhancing resilience, and fostering a trustworthy environment, ultimately contributing to organizational freedom and operational efficiency.
Key Features of Secure IT Infrastructure 516150359
Key features of secure IT infrastructure play a pivotal role in safeguarding an organization’s digital assets and ensuring operational continuity.
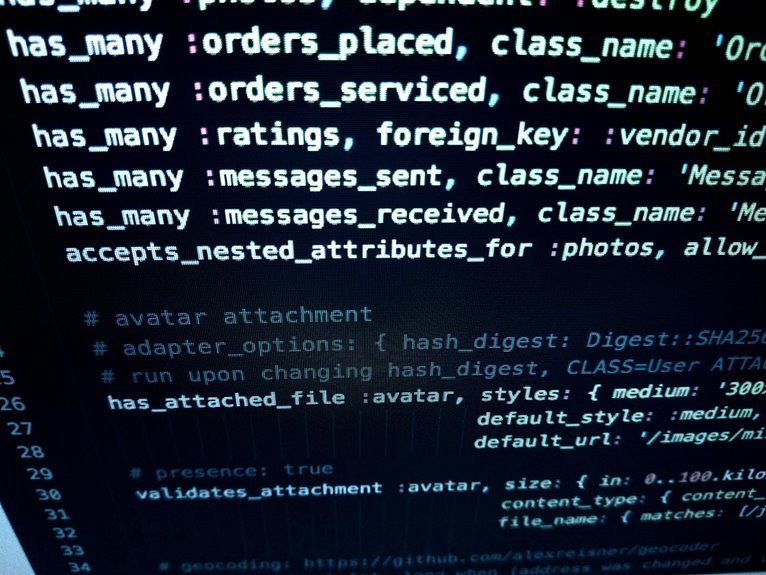
Effective network segmentation limits exposure to threats by isolating sensitive data, while robust access controls enforce user permissions, minimizing unauthorized access.
Together, these features create a resilient framework that enhances security measures, empowering organizations to maintain operational integrity and protect critical information.
How Does Secure IT Infrastructure 516150359 Enhance Cybersecurity?
How can a secure IT infrastructure substantially enhance an organization’s cybersecurity posture?
By integrating advanced threat detection mechanisms and robust risk management strategies, such infrastructure fortifies defenses against potential breaches.
It systematically identifies vulnerabilities, enabling proactive measures.
Consequently, organizations can mitigate risks effectively, ensuring data integrity and confidentiality while fostering a resilient environment that aligns with the principles of autonomy and freedom in digital operations.
Steps to Implement Secure IT Infrastructure 516150359 in Your Organization
Implementing a secure IT infrastructure requires a systematic approach that encompasses various critical steps. Organizations should begin with a thorough risk assessment to identify vulnerabilities.
Following this, adopting best practices, such as regular software updates, strong access controls, and employee training, ensures ongoing security.
Continuous monitoring and incident response plans are essential to maintain resilience against evolving threats, safeguarding both data and organizational integrity.
Conclusion
In conclusion, Secure IT Infrastructure 516150359 is essential for safeguarding sensitive data and maintaining operational continuity in an increasingly digital landscape. The integration of robust security measures, such as effective network segmentation and advanced threat detection, significantly reduces the risk of breaches. Notably, organizations that implement comprehensive security frameworks experience 50% fewer incidents of data loss, underscoring the critical importance of a well-structured IT infrastructure in enhancing overall cybersecurity resilience and operational efficiency.